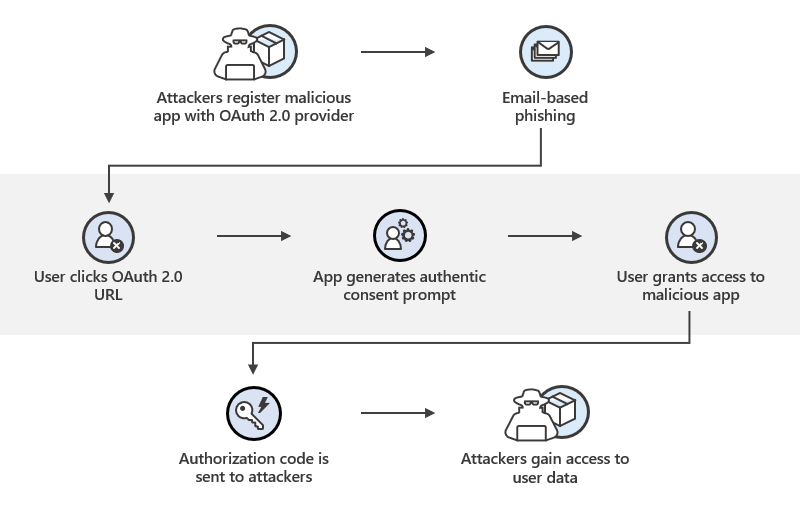
How “legitimate” integrations quietly become breach paths
OAuth is designed to make integrations safe and simple.
In practice, OAuth tokens are one of the most abused assets in modern SaaS environments — especially when they are issued, stored, or used in the browser.
This Attack of the Week breaks down how OAuth token abuse actually happens, why it bypasses traditional security controls, and where detection usually fails.
Executive Summary
- Attack type: OAuth token abuse via browser execution
- Target: SaaS data, user accounts, downstream APIs
- Impact: Silent data access, persistence, lateral movement
- Detection gap: OAuth is “working as designed”
No credentials stolen.
No MFA bypassed.
No alerts triggered.
Phase 1: User Grants OAuth Consent (Nothing Malicious Yet)
The attack begins with a normal user action:
- Clicking “Sign in with …”
- Connecting a productivity tool
- Authorizing a browser-based integration
The consent screen looks legitimate.
Permissions appear reasonable.
The user approves.
From a security perspective, this is expected behavior.
Phase 2: Token Issuance in a Hostile Environment
OAuth access tokens are often:
- Returned to browser-based apps
- Stored in memory or storage
- Used by JavaScript to call APIs
At this moment:
- The token exists in a hostile runtime
- Third-party scripts already execute
- Extensions can observe behavior
The risk begins after consent, not during it.
Phase 3: Token Observation or Replay
Malicious code does not need to steal credentials.
It can:
- Observe token values in memory
- Hook API calls using the token
- Replay authorized requests
- Reuse refresh tokens for persistence
All activity is fully authorized.
Phase 4: Silent, Ongoing Data Access
OAuth abuse often looks like:
- Normal API calls
- Expected scopes
- Legitimate endpoints
- Low-volume traffic
Because OAuth is designed for automation, this abuse blends in perfectly.
Why Traditional Controls Miss This
MFA
MFA protects login — not token usage.
WAF / API Gateways
Tokens are valid. Requests are authorized.
SIEM
Logs show normal OAuth activity.
SSPM
Focuses on tenant configuration, not browser execution.
Nothing appears broken.
Why OAuth Abuse Is Harder Than JWT Theft
OAuth tokens:
- Are expected to be used programmatically
- Often have long lifetimes
- Are rarely monitored per user
- Persist beyond browser sessions
This makes them ideal for long-term abuse.
Common Real-World Triggers
OAuth abuse often starts from:
- Browser extensions
- Shadow SaaS tools
- Embedded widgets
- Compromised third-party scripts
- Internal “temporary” integrations
None of these require exploitation.
Where Early Detection Was Possible
This attack could have been detected during:
- Unexpected browser-side API usage
- New execution paths touching OAuth flows
- Token usage outside normal UI behavior
- Runtime behavior drift after consent
These signals occur before data abuse is noticed.
How BreachFin Detects OAuth Abuse Early
BreachFin focuses on execution context, not token theory.
BreachFin can:
- Detect client-side execution paths interacting with OAuth tokens
- Identify unexpected script behavior near consent and token usage
- Surface browser-side anomalies before API abuse scales
- Provide evidence of unauthorized client-side behavior
This brings OAuth risk out of the “working as intended” blind spot.
Why This Matters for SaaS Security
OAuth abuse:
- Bypasses identity controls
- Persists silently
- Scales across users
- Is difficult to revoke surgically
Most organizations discover it months later, during audits or investigations.
Lessons Learned
- OAuth tokens are not inherently safe in browsers
- Consent does not equal safety
- Authorization ≠ legitimacy
- Runtime context matters more than protocol correctness
Final Takeaway
OAuth did exactly what it was designed to do.
The failure occurred in assuming:
“If it’s authorized, it must be safe.”
In modern SaaS environments, authorization is not the same as trust.
If your security program cannot see:
- How OAuth tokens are used in the browser
- What code touches them
- Whether execution matches intent
Then OAuth becomes a blind spot — not a control.
This is why BreachFin treats browser execution as a first-class security surface.
