How marketing tools become an attacker’s delivery pipeline
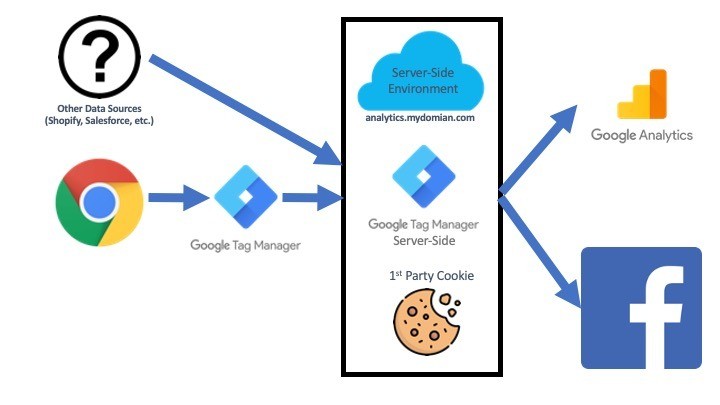
Tag managers are powerful.
They allow marketing teams to:
- Add scripts without deployments
- Run experiments
- Track conversions
- Modify UI behavior
- Integrate external vendors
They also allow attackers to:
- Inject JavaScript
- Modify the DOM
- Redirect users
- Capture sensitive data
- Bypass security controls
All without touching your backend.
This edition of Attack of the Week explains how tag managers become a silent attack vector — and why organizations consistently underestimate the risk.
Why Tag Managers Are High-Risk
Because they:
- Sit outside engineering review
- Are controlled by non-technical teams
- Load scripts dynamically and silently
- Often bypass CSP and SRI
- Execute with full DOM access
- Are trusted implicitly
A single misconfiguration can expose your entire funnel.
Phase 1: Tag Manager Access Is Obtained
Attackers gain access via:
- Stolen marketer credentials
- Shared accounts with weak passwords
- Phishing
- Supply-chain compromise of a vendor
- Internal misconfiguration
Because tag managers are not treated as high-security systems, access controls are often weak.
Phase 2: Malicious Script Is Added or Modified
The attacker:
- Injects a new JavaScript snippet
- Modifies an existing tag
- Adds a redirect rule
- Creates a new container version
Marketing teams may assume it’s part of a campaign.
Security never sees the update.
Phase 3: Script Executes Silently in the Browser
The injected script:
- Loads during normal user sessions
- Acts within trusted domains
- Uses legitimate browser APIs
- Runs after authentication
No backend alert is triggered.
Phase 4: Data Collection Begins
Malicious code captures:
- Form inputs
- Billing info
- Session cookies
- JWTs or OAuth tokens
- User behavior data
Often, exfiltration is disguised as analytics traffic.
Phase 5: Traffic or Payments Are Manipulated
Attackers can:
- Redirect users to fake payment pages
- Modify checkout behavior
- Inject fraudulent fields
- Alter API endpoints in the browser
- Skim card or identity data
All of this happens before your backend receives a request.
Why Tag Manager Attacks Are So Effective
1. They Don’t Break Anything
Users still see a working page.
Marketing goals still track.
Engineering sees no errors.
2. They Bypass Traditional Security
WAFs, SIEMs, and backend logs see only valid traffic.
3. They Abuse Trusted Execution Paths
Tag manager scripts are approved by design.
4. They Require No Code Deployment
The compromise bypasses CI/CD and engineering review entirely.
Why CSP and SRI Don’t Save You Here
CSP fails because:
- Tag managers require permissive rules
- Dynamic scripts bypass source restrictions
SRI fails because:
- Tag manager scripts are dynamic
- Hashes cannot be applied to unpredictable content
Neither control can prevent runtime injection by design.
Real-World Breach Pattern
This attack is common across:
- E-commerce sites
- Fintech apps
- Subscription platforms
- Online banking UIs
- SaaS dashboards
In many cases:
- Fraud occurred for months
- Backend remained uncompromised
- Tag manager changes were never audited
Where Detection Was Possible
Early detection could have caught:
- New script loaded from unexpected domain
- DOM modifications on sensitive pages
- Changes in redirect logic
- Event listeners added near payment inputs
- New outbound traffic destinations
But without browser runtime monitoring, these signals are invisible.
How BreachFin Detects Tag Manager Attacks
BreachFin monitors:
- Client-side script execution paths
- DOM and behavior drift
- Unexpected network calls
- Unauthorized runtime modifications
BreachFin alerts when:
- New scripts appear unexpectedly
- Script behavior changes from baseline
- Sensitive elements gain new listeners
- Redirect logic is altered
This enables detection before fraud happens.
What Security Teams Must Change
Tag managers must be treated as:
- Security-critical systems
- Privileged execution sources
- Potential breach points
Security needs:
- Access controls
- Audit trails
- Runtime monitoring
- Alerts on drift
Without visibility, tag managers become invisible attack pipelines.
Final Takeaway
Tag managers are powerful — for both marketers and attackers.
Because they:
- Execute trusted scripts
- Bypass engineering controls
- Operate outside traditional monitoring
- Modify the browser at runtime
If your security program ignores tag manager behavior,
you are leaving a high-privilege, high-impact vector unmonitored.
This is why BreachFin treats tag managers as part of the security perimeter —
not just a marketing tool.
