Modern attacks do not begin with exploits—they begin with exposure. Untracked assets, misconfigurations, and weak trust boundaries give attackers a head start long before a breach is detected.
BreachFin is designed to eliminate that blind spot. Our platform continuously discovers, analyzes, and simulates real-world attack paths across your external environment—without disrupting production systems.
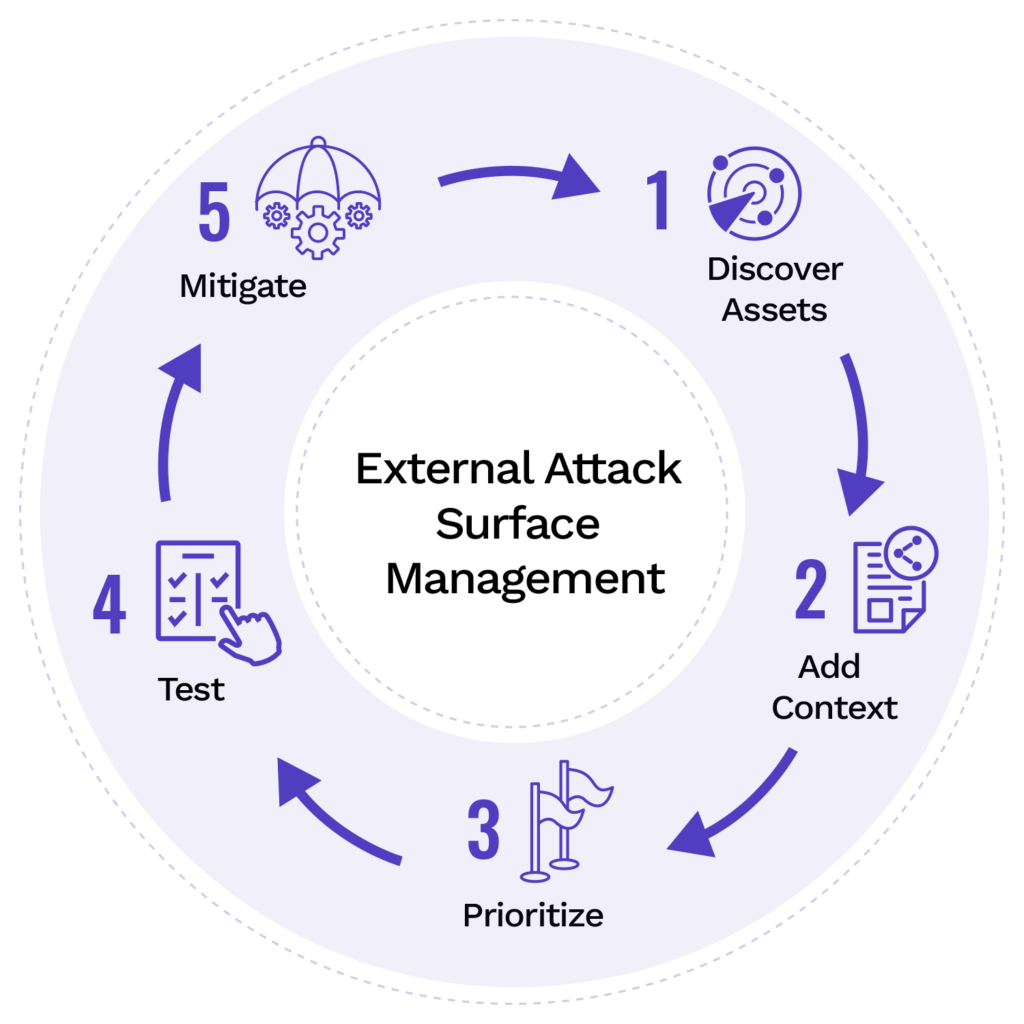
Below is how BreachFin delivers end-to-end external attack surface and exploitation visibility.
1. Automated External Attack Surface Discovery
Your organization’s attack surface is constantly changing. New domains, cloud services, APIs, and third-party integrations appear faster than traditional inventories can keep up.
BreachFin continuously maps and monitors all public-facing assets, including:
- Domains and subdomains
- Exposed IP ranges and cloud endpoints
- Open ports and running services
- TLS/SSL configuration weaknesses
- Web server and application framework fingerprints
- Newly introduced or unauthorized internet-facing components
By maintaining a live inventory of your external footprint, BreachFin ensures security teams always know what is exposed, where it lives, and how it is reachable—before attackers do.
2. Continuous Vulnerability & Misconfiguration Scanning
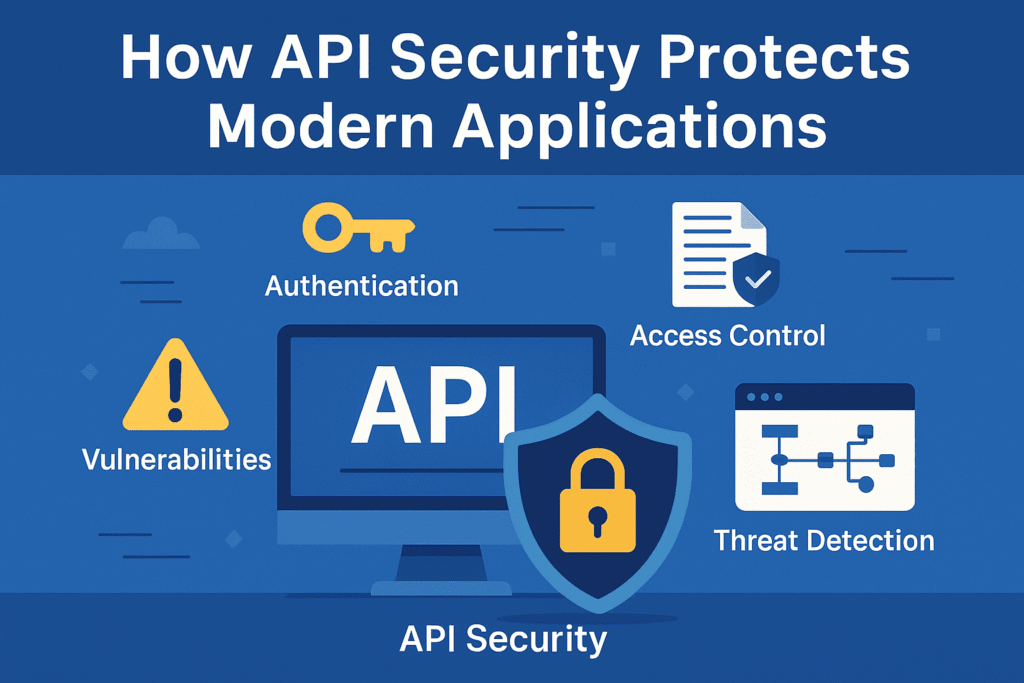
Discovery alone is not enough. Exposure becomes risk when weaknesses exist.
BreachFin performs continuous, non-intrusive security testing to identify vulnerabilities and misconfigurations such as:
- OWASP Top 10 web application risks
- API authentication and authorization flaws
- Security header misconfigurations (CSP, HSTS, etc.)
- Outdated, vulnerable, or exposed server components
- Broken access controls and session handling issues
- Weak or missing rate-limiting protections
All scans are designed to be safe for production environments, enabling continuous monitoring without operational impact.
The result is actionable visibility into real security gaps—not just static findings.
3. Intelligent Exploit-Path Simulation
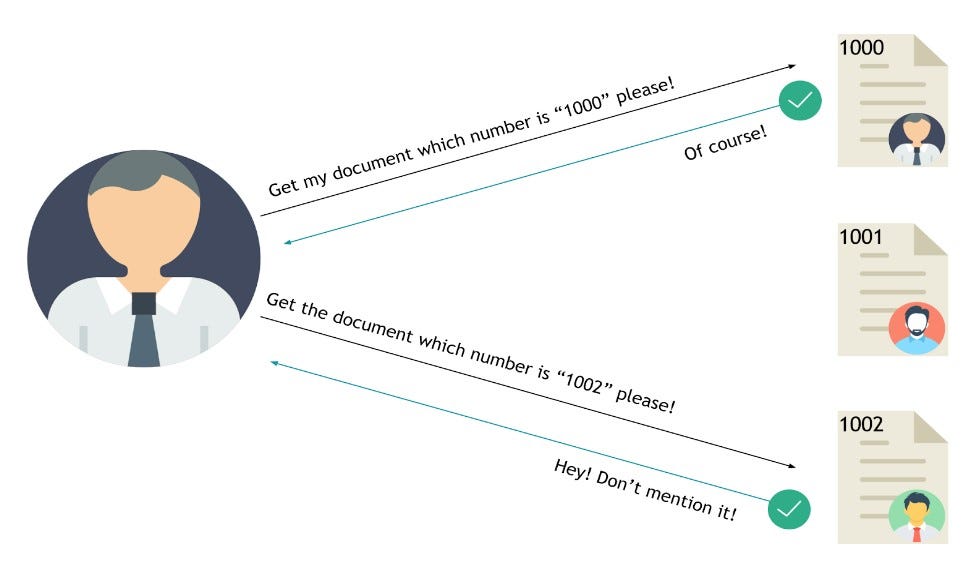
Knowing a vulnerability exists is useful. Knowing how it can be exploited is critical.
BreachFin goes beyond scanning by simulating real-world attacker behavior to validate exploitability, including:
- Authentication bypass attempts
- Broken access control and IDOR validation
- JWT tampering and token replay detection
- Path traversal and input mutation testing
- Session fixation analysis
- API privilege escalation simulations
These simulations model how attackers chain weaknesses together—without exploiting systems destructively—so teams can prioritize remediation based on real attack paths, not theoretical risk.
Why BreachFin
BreachFin delivers continuous external security visibility by combining discovery, scanning, and exploit-path intelligence into a single platform. This allows security teams to:
- Reduce unknown and unmanaged exposure
- Prioritize fixes based on real-world risk
- Detect drift and misconfigurations early
- Strengthen security posture without slowing development
Security is not a one-time assessment. BreachFin ensures it is continuous, contextual, and actionable.
