Why trusted add-ons quietly undermine web security
Browser extensions are often treated as harmless productivity tools. In reality, they represent one of the most powerful and least monitored attack surfaces in modern web applications.
Extensions do not need to exploit vulnerabilities.
They are granted access by design.
Why Browser Extensions Are So Dangerous
Extensions can be:
- Installed by users
- Pushed by enterprises
- Updated silently
- Granted broad permissions
Once installed, many extensions can:
- Read and modify DOM content
- Observe form inputs
- Intercept network requests
- Access cookies or storage
- Inject scripts into pages
All of this happens outside your application’s control.
The Trust Problem No One Owns
Security teams assume:
- Browsers are managed by IT
- Extensions are vetted
- Users act responsibly
Reality:
- Personal extensions coexist with corporate apps
- Permission prompts are ignored
- Updates change behavior post-approval
- Shadow extensions proliferate unnoticed
There is often no owner for extension risk.
How Extensions Bypass Traditional Security
Extensions operate in a privileged layer:
- Above JavaScript application logic
- Outside backend visibility
- Independent of WAFs and CSPs
Even strong CSP policies:
- Cannot block extension-injected scripts
- Cannot prevent content scripts
- Cannot restrict extension APIs
From a security standpoint, extensions are effectively trusted insiders.
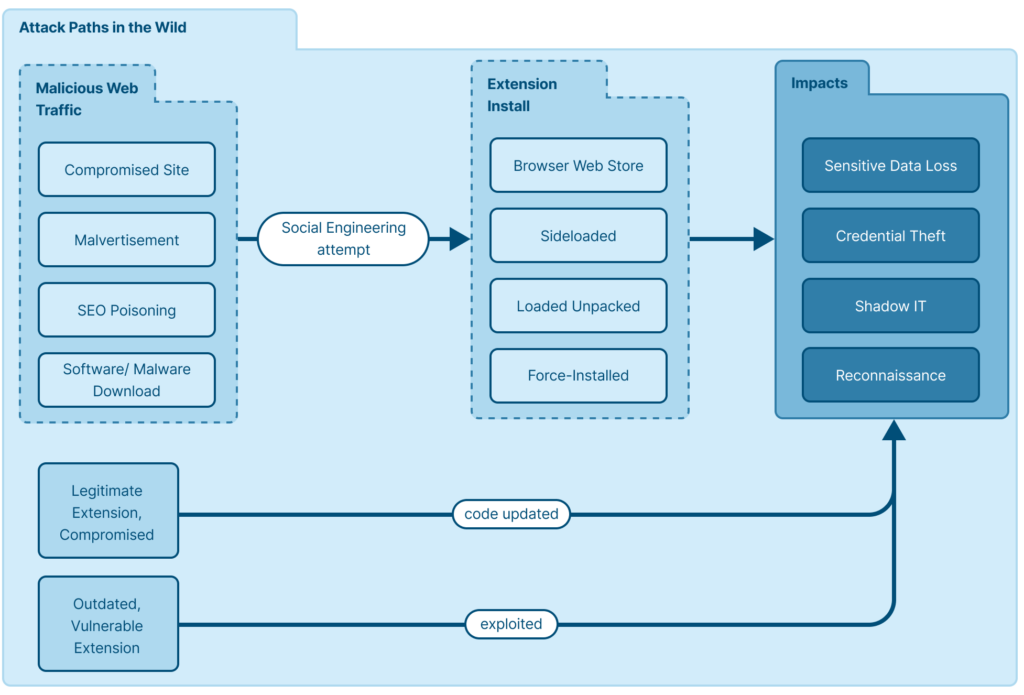
Extension-Based Attack Flow
Step 1: Extension Is Installed or Updated
This may occur via:
- User installation
- Enterprise policy
- Automatic update
The change may be invisible.
Step 2: Content Script Executes
The extension injects JavaScript into:
- Login pages
- Dashboards
- Payment flows
The script runs with access to the DOM and user context.
Step 3: Sensitive Data Is Observed
Common targets:
- JWTs and session tokens
- Form fields
- Payment data
- Application logic flows
No exploit is required.
Step 4: Data Is Exfiltrated
The extension communicates with:
- Its own backend
- A compromised update endpoint
- An attacker-controlled service
All traffic appears legitimate.
Why This Matters for JWT and Sessions
Extensions can:
- Hook
fetchand XHR - Read Authorization headers
- Observe token refresh flows
- Replay authenticated actions
MFA, Zero Trust, and backend validation all pass.
The browser is compromised, not the identity.
Compliance Implications
Browser extension risk affects:
- PCI DSS 4.0 client-side controls
- SOC 2 logical access assurance
- Data protection obligations
- Insider threat models
Yet extensions rarely appear in:
- Threat models
- Audit discussions
- Incident response plans
This is a growing compliance blind spot.
Why “Managed Browsers” Are Not Enough
Enterprise browser policies help, but:
- Personal devices remain in scope
- BYOD expands exposure
- Users bypass restrictions
- Extensions update dynamically
Policy does not equal visibility.
What Real Defense Looks Like
Defending against extension-based attacks requires:
- Monitoring runtime client-side behavior
- Detecting unexpected DOM or script interactions
- Identifying execution anomalies
- Understanding how sessions are actually used
Blocking alone is insufficient.
How BreachFin Helps
BreachFin provides visibility into:
- What executes in the browser
- How execution changes over time
- When client-side behavior deviates from baseline
This allows detection of:
- Extension-driven anomalies
- Silent script injection
- Token exposure patterns
Even when the extension itself is unknown.
Why This Attack Surface Is Growing
Extensions are increasing because:
- Remote work is normal
- SaaS adoption is exploding
- Productivity tooling is browser-first
- Security ownership is fragmented
Attackers follow convenience.
Final Takeaway
Browser extensions are powerful, persistent, and largely invisible.
They:
- Bypass backend security
- Ignore CSP boundaries
- Operate post-authentication
- Exploit trust, not vulnerabilities
If your security model does not account for browser extensions,
it is incomplete by default.
Modern web security requires visibility where extensions live —
inside the browser runtime.
That is the layer BreachFin is designed to illuminate.
