How trusted scripts become your biggest security liability
When organizations think about supply chain risk, they picture compromised packages, poisoned dependencies, or malicious updates pushed through CI/CD pipelines.
In reality, one of the most exploited supply chains today runs directly inside the browser.
Client-side supply chain attacks do not target your servers.
They target the JavaScript you trust.
What Is a Client-Side Supply Chain Attack?
A client-side supply chain attack occurs when an attacker compromises:
- A third-party JavaScript library
- A CDN-hosted script
- A tag manager or analytics tool
- A marketing, chat, or A/B testing script
That script then executes inside your users’ browsers, with the same privileges as your own application code.
No backend breach is required.
Why These Attacks Are So Effective
Client-side supply chain attacks succeed because they exploit implicit trust.
Once a script is allowed to run:
- It can access the DOM
- It can hook
fetchandXMLHttpRequest - It can observe form inputs
- It can intercept authentication flows
- It can read or relay tokens and session data
From the backend’s point of view, nothing is wrong.
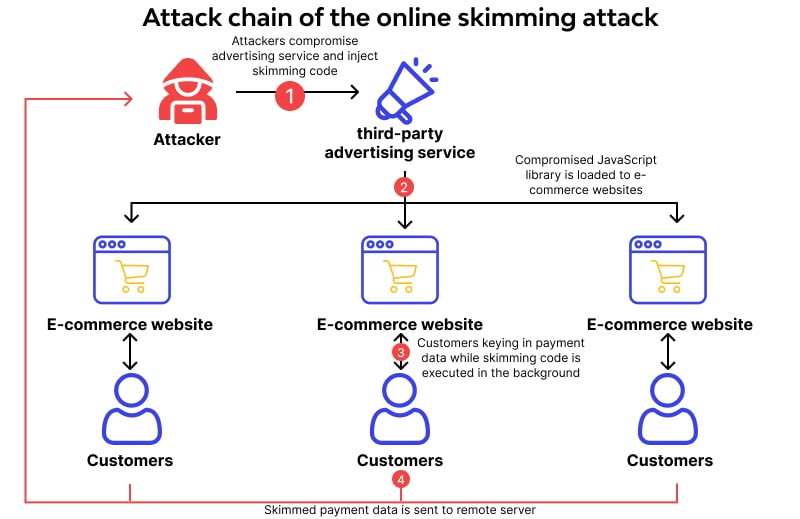
The Typical Attack Flow
Step 1: Trusted Script Is Compromised
Attackers compromise:
- A vendor’s CDN
- A dependency update
- A third-party SaaS integration
- An unused but still-loaded script
The change may be small — often just a few obfuscated lines.
Step 2: Malicious Code Executes in the Browser
The script:
- Loads silently
- Blends in with existing logic
- Executes on real user sessions
There is no exploit payload, no scanning noise, no alert.
Step 3: Sensitive Data Is Captured
Common targets include:
- Payment form fields
- Authentication tokens (JWTs, sessions)
- Personally identifiable information
- User behavior and metadata
All captured after authentication.
Step 4: Data Is Exfiltrated
The script sends data to:
- Attacker-controlled endpoints
- Lookalike domains
- Abused analytics or logging endpoints
This often bypasses backend detection entirely.
Why Traditional Security Tools Miss This
WAFs and API Gateways
- Only see incoming requests
- Cannot inspect browser-side execution
- Trust valid tokens and sessions
SAST / DAST
- Analyze code at rest
- Do not see runtime script changes
- Miss injected or dynamically loaded code
CSP (Alone)
- Helps, but drifts over time
- Cannot detect trusted script behavior changes
- Often loosened to “fix” breakages
These tools were not designed to monitor runtime client-side behavior.
The Magecart Lesson (Still Relevant)
Magecart-style attacks demonstrated a critical truth:
You do not need to breach the payment processor if you can observe the payment form.
The same principle now applies to:
- Authentication
- JWTs
- SaaS dashboards
- Admin portals
- Any browser-based workflow
If it runs in the browser, it is part of the attack surface.
Why “We Only Use Reputable Vendors” Is Not a Defense
Reputable vendors:
- Get compromised
- Push buggy updates
- Change script behavior
- Add new dependencies
- Introduce tracking or data flows over time
Trust is not static.
Execution is dynamic.
Without visibility, drift becomes breach.
The Compliance Blind Spot
Client-side supply chain attacks directly impact:
- PCI DSS 4.0 client-side tamper detection
- SOC 2 logical access controls
- Data protection and privacy obligations
Passing an audit does not mean:
- Scripts haven’t changed
- Execution hasn’t drifted
- Tokens aren’t exposed
Auditors increasingly expect continuous monitoring, not periodic checks.
How BreachFin Addresses Client-Side Supply Chain Risk
BreachFin focuses on what actually executes in the browser, not just what is configured.
BreachFin enables teams to:
- Monitor client-side script execution
- Detect unauthorized script changes
- Identify unexpected DOM and behavior drift
- Catch early indicators of supply chain compromise
This shifts detection before fraud, not after.
Why This Matters Now
Client-side attacks are attractive because they:
- Bypass backend defenses
- Scale silently
- Use legitimate traffic
- Are difficult to attribute
- Often go undetected for months
As applications become more browser-driven, this attack class will continue to grow.
Final Takeaway
Client-side supply chain attacks do not exploit vulnerabilities.
They exploit trust.
If your security strategy does not include:
- Browser execution visibility
- Detection of script changes
- Monitoring of runtime behavior
Then your most trusted code may already be your weakest link.
This is the modern web security reality —
and the problem BreachFin is designed to solve.
