Why outsourcing the payment page does not outsource responsibility
One of the most common — and dangerous — assumptions in web security is:
“We use a hosted payment page, so client-side attacks aren’t our problem.”
This belief is widespread.
It is also wrong.
This blog breaks down why hosted payments do not eliminate client-side risk, how attackers exploit the surrounding browser flow, and why auditors increasingly challenge this assumption.
Where the Myth Comes From
Hosted payment models promise:
- Reduced PCI scope
- No card data stored on your servers
- Offloaded payment processing
- Simplified compliance
All of that is partially true.
What gets overlooked is how users reach the hosted page — and what executes before, during, and after that transition.
The Browser Does Not Reset Trust
When a user clicks “Pay Now”:
- They are already in your browser context
- Your scripts are already executing
- Third-party code is already loaded
- The DOM is already manipulable
Attackers do not need to touch the hosted page itself.
They only need to influence the flow around it.
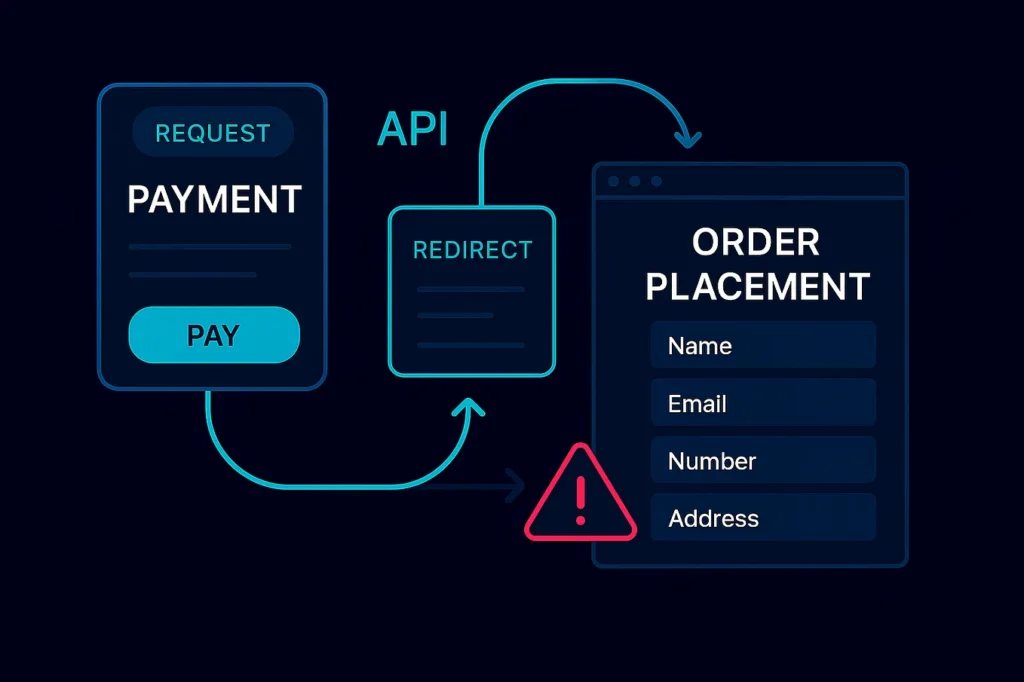
The Real Client-Side Attack Surface
Even with hosted payments, your application still controls:
- The checkout page
- Redirect logic
- Embedded scripts
- UI elements and event handlers
- Pre-payment data collection
If malicious code runs here, it can:
- Modify redirect destinations
- Capture data before handoff
- Inject additional fields
- Observe user behavior
- Steal tokens or metadata
No card processor breach required.
Common Hosted-Payment Attack Patterns
1. Redirect Manipulation
Injected scripts alter:
- Payment URLs
- Parameters
- Destination domains
Users believe they are paying securely — they are not.
2. Pre-Payment Data Capture
Attackers capture:
- Billing information
- User identity data
- Session tokens
- Order metadata
This data is monetized even without card numbers.
3. UI Injection
Malicious scripts:
- Add fake fields
- Overlay trusted UI
- Trick users into entering sensitive data
All before reaching the hosted provider.
4. Token and Session Abuse
Valid sessions are:
- Observed
- Replayed
- Used to automate fraud
Authentication already succeeded.
Why Backend and Payment Providers Don’t See This
Payment providers:
- Secure their own pages
- Do not monitor your browser execution
- Have no visibility into your scripts
Your backend:
- Sees valid redirects
- Receives legitimate callbacks
- Processes successful transactions
Everyone thinks everything is fine.
What Auditors Actually Expect Now
Modern audits — especially under PCI DSS 4.0 — focus on intent, not loopholes.
Auditors ask:
- How do you detect unauthorized script changes?
- What runs before redirect?
- How do you know the flow wasn’t manipulated?
- What evidence proves continuous monitoring?
“Hosted” does not mean “out of scope”.
Why This Myth Is Actively Dangerous
Believing hosted payments eliminate risk leads to:
- No client-side monitoring
- Blind trust in third-party scripts
- Weak CSP enforcement
- No detection between scans
This is exactly where attackers operate.
How BreachFin Fits Into Hosted Payment Models
BreachFin does not replace your payment provider.
It protects the browser execution environment leading to it.
BreachFin helps teams:
- Monitor scripts on checkout and redirect pages
- Detect unauthorized DOM or behavior changes
- Identify manipulation before payment handoff
- Provide audit-ready evidence of control effectiveness
This closes the gap hosted payments leave open.
The Compliance Reality
Hosted payments reduce scope.
They do not remove responsibility.
If your application:
- Executes JavaScript
- Handles user interaction
- Controls redirects
- Loads third-party scripts
Then client-side risk still exists — and must be addressed.
Final Takeaway
Hosted payments secure where money is processed.
They do not secure how users get there.
Attackers exploit the journey, not the destination.
If your security or compliance strategy assumes:
“Hosted equals safe”
Then your most critical flow is operating without visibility.
Client-side risk does not disappear —
it simply moves earlier in the browser execution path.
That is precisely the layer BreachFin is designed to protect.
