Why audits validate paperwork — not runtime reality
Passing an audit feels like winning.
Controls reviewed. Evidence accepted. Report signed.
Then a breach happens.
This is not bad luck. It is a category error — confusing audit assurance with operational security.
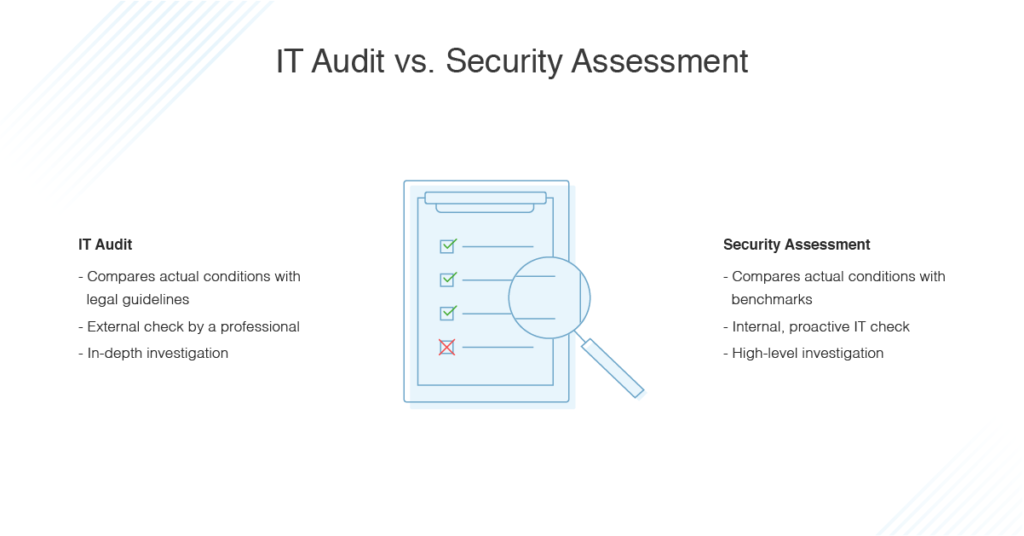
What Audits Are Actually Designed to Do
Audits answer a narrow question:
“At a point in time, did your controls exist and align with the framework?”
They are excellent at validating:
- Policy presence
- Control design
- Process documentation
- Sample-based evidence
- Intent to comply
They are not designed to:
- Monitor runtime behavior
- Detect client-side execution drift
- Catch short-lived attacks
- Validate real-user execution paths
Audits are snapshots. Attacks are continuous.
The Gap Audits Cannot Close
Modern applications change constantly:
- Scripts update without deployments
- Third parties alter behavior
- CSP exceptions accumulate
- Browser execution evolves daily
Between audit checkpoints:
- Trust assumptions drift
- Attack windows open
- Controls degrade silently
Passing an audit does not freeze reality.
Why “Audit-Approved” Systems Still Get Breached
Common post-audit breach patterns include:
1. Runtime-Only Attacks
- Script injected for hours or days
- Removed before next review
- Never appears in evidence
Audit: clean
Reality: compromised
2. Trusted Code Turns Malicious
- Vendor update introduces risky logic
- CSP still allows the source
- SRI not applicable
- Behavior changes, config doesn’t
Audit: compliant
Reality: unsafe
3. Browser-Side Abuse Post-Authentication
- MFA succeeds
- JWT issued
- Client-side code abuses session
- Backend logs show normal traffic
Audit: controls passed
Reality: trust abused
Why Frameworks Are Evolving (But Slowly)
Frameworks like PCI DSS 4.0 are shifting toward:
- Continuous detection
- Client-side monitoring
- Tamper detection
- Runtime awareness
But audits still rely on:
- Evidence sampling
- Time-bounded validation
- Documentation
This creates a lag attackers exploit.
The Dangerous Language Trap
Organizations often say:
- “We’re compliant”
- “We passed”
- “Audit didn’t find issues”
Attackers hear:
- “No one is watching runtime”
- “Drift will go unnoticed”
- “Detection is periodic”
This is not negligence — it’s structural.
Compliance vs Security: The Correct Relationship
Compliance should be:
- A floor, not a ceiling
- Evidence of intent, not proof of safety
- Backed by operational controls
Security must:
- Observe reality
- Detect drift
- Alert early
- Operate continuously
When compliance replaces security, risk spikes.
What Auditors Increasingly Ask Next
Forward-looking auditors now ask:
- How do you detect unauthorized changes?
- What happens between scans?
- Can you show alerts, not screenshots?
- How do you know controls stayed effective?
These questions point directly at runtime visibility gaps.
How BreachFin Changes the Audit Conversation
BreachFin doesn’t replace audits.
It makes audit claims defensible.
BreachFin provides:
- Continuous evidence of client-side control effectiveness
- Detection records instead of assumptions
- Runtime visibility aligned with framework intent
- Proof that trust hasn’t been abused since the last audit
This turns audits from a risk reset into a checkpoint.
The Operational Truth
Most breaches do not indicate:
- Missing controls
- Bad intentions
- Audit failure
They indicate:
- Unobserved drift
- Runtime blind spots
- False confidence
Security fails quietly between successful audits.
Final Takeaway
Passing an audit means:
“Controls existed when checked.”
It does not mean:
“Controls worked continuously.”
If your security posture relies on:
- Periodic validation
- Static evidence
- Assumed trust
Then your highest-risk periods are completely unmonitored.
Modern security requires continuous visibility —
so audits confirm reality instead of masking its absence.
That is the difference between being compliant
and being secure.
