Most JWT documentation focuses on how to issue tokens.
Most breaches happen after tokens are issued.
This blog takes a deeper, technical look at where JWT security actually fails in production environments and how BreachFin addresses the blind spots traditional JWT implementations ignore.
JWT Is Cryptographically Sound — Operationally Fragile
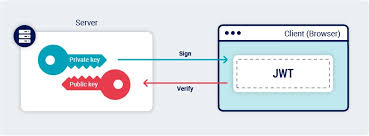
From a cryptographic perspective, JWT is solid:
- Strong signing algorithms (RS256 / ES256)
- Verifiable integrity
- Stateless validation
- Scales cleanly across services
Yet JWT is involved in:
- Account takeovers
- Fraud campaigns
- Session hijacking
- Large-scale SaaS breaches
Why?
Because JWT assumes the execution environment is trustworthy.
In modern web applications, that assumption is wrong.
The Hidden JWT Attack Surface
JWT’s real attack surface is not the token format — it’s where the token lives and executes.
1. Browser-Resident Tokens
In SPAs and modern SaaS apps:
- JWTs are stored in memory, cookies, or storage
- Executed inside a hostile environment
- Exposed to third-party scripts
Once a token is readable, encryption and signing no longer matter.
2. Client-Side Supply Chain Risk
Modern pages load:
- Analytics scripts
- Tag managers
- Chat widgets
- A/B testing frameworks
- Payment libraries
Any compromised script can:
- Read JWTs
- Hook XHR / fetch
- Exfiltrate Authorization headers
- Proxy authenticated requests
This is how token theft happens silently.
3. Shadow Integrations and Extensions
JWTs are often exposed to:
- Browser extensions
- OAuth-connected SaaS tools
- Unapproved plugins
- Internal “temporary” integrations
These paths rarely appear in architecture diagrams — but attackers find them quickly.
Why Backend JWT Best Practices Are Not Enough
Even a “perfect” backend JWT implementation still fails if:
- Tokens are accessible to JavaScript
- CSP is misconfigured
- Third-party scripts change behavior
- Extensions inject content scripts
- Shadow IT expands token exposure
Backend controls cannot see this.
This is the JWT visibility gap.
BreachFin’s JWT-Centric Security Model
BreachFin focuses on where JWTs are most often compromised: the browser.
1. Browser Execution Visibility
BreachFin monitors:
- What scripts execute
- Where they originate
- What changes over time
This enables detection of:
- New scripts accessing sensitive execution paths
- Unexpected client-side behavior
- Supply chain modifications
2. Client-Side Tamper Detection
JWT theft often begins with small, silent changes:
- Injected script
- Modified loader
- Altered inline code
BreachFin detects:
- DOM mutations
- Script integrity drift
- Unauthorized client-side changes
Before tokens are abused.
3. Token Exposure Risk Reduction
BreachFin helps security teams:
- Identify risky token handling patterns
- Detect scripts capable of intercepting JWTs
- Reduce browser-side blast radius
This is critical for:
- PCI DSS 11.6.1
- SOC 2 logical access controls
- SaaS supply chain security
JWT, PCI DSS, and Modern Compliance
JWT misuse directly impacts compliance controls:
- Authentication assurance
- Session integrity
- Protection against account misuse
- Client-side tampering detection
PCI DSS 4.0 explicitly acknowledges:
- Browser-based attacks
- Script injection risks
- Client-side compromise paths
JWT security is now a browser security problem, not just an API concern.
A Secure JWT Architecture (Modern Reality)
A hardened JWT architecture includes:
Backend
- Short-lived access tokens
- Strong asymmetric signing
- Strict claim validation
- Refresh token rotation
Frontend
- Minimal token exposure
- Strong CSP enforcement
- Reduced third-party script access
- Continuous client-side monitoring
BreachFin operates squarely in the frontend half — the part most teams overlook.
Why JWT Breaches Are Hard to Detect Without BreachFin
JWT abuse often looks like:
- Normal authenticated traffic
- Valid tokens
- Legitimate API calls
- Correct user context
Traditional tools see nothing wrong.
BreachFin detects the precursor events:
- Script changes
- Execution anomalies
- Unauthorized browser behavior
This shifts detection left of fraud and breach.
Final Takeaway
JWT is not broken.
JWT assumptions are.
In modern web applications:
- Tokens live in hostile environments
- Attackers target browsers, not crypto
- Visibility gaps enable silent compromise
BreachFin closes that gap by protecting JWTs where they actually fail — in the browser, at runtime, inside the client-side execution path.
If your authentication relies on JWT,
your security strategy must extend beyond the backend.
