The most underrated browser security header — and why it matters more in 2026
Most people know CSP. Some know SRI. Few know Permissions-Policy — the header that controls access to high-risk browser features such as camera, microphone, geolocation, clipboard, fullscreen, and powerful APIs that can be abused by malicious scripts, browser extensions, or compromised third-party code.
Yet Permissions-Policy is often missing entirely, configured incorrectly, or treated as optional.
This deep-dive explains what it actually does, why it is critical for modern client-side security, and how it pairs with BreachFin to protect your frontend environment in ways CSP cannot.
1. What Permissions-Policy Actually Controls
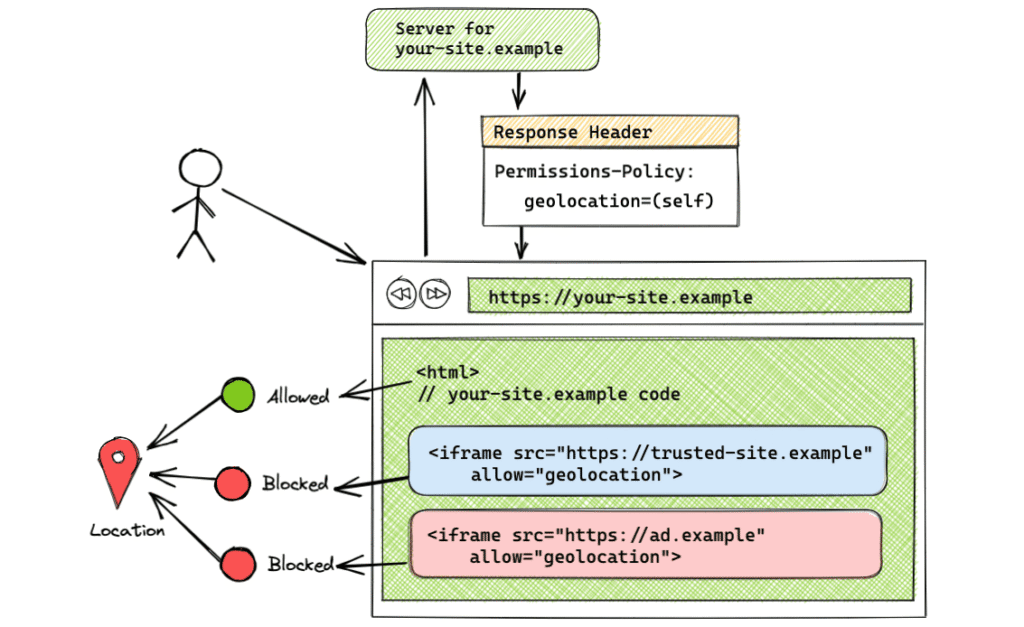
Permissions-Policy (formerly Feature-Policy) regulates which origins can use powerful browser features.
Here are some capabilities it can restrict:
High-risk browser features
cameramicrophonegeolocationclipboard-readclipboard-writepaymentpublickey-credentials-getscreen-wake-lock
High-impact APIs often abused
fullscreenautoplayaccelerometergyroscopemagnetometerusbbluetoothserialhidmidi
These APIs allow intrusive data access or unexpected device interaction.
Without Permissions-Policy, any script — trusted or malicious — can attempt to use these APIs.
2. Why Permissions-Policy Matters More in 2026
The modern web now includes:
- AI assistants scraping screen data
- Browser extensions injecting UI elements
- Third-party payment widgets
- Identity flows involving WebAuthn
- OAuth apps requesting clipboard access
- Productivity tools reading user content
Attackers no longer rely on exploit chains — they rely on available APIs.
Permissions-Policy blocks many of those APIs outright.
3. Why Many Organizations Misconfigure It
Common mistakes include:
1. Leaving it out entirely
Most sites do not set Permissions-Policy at all.
2. Using wildcards
Example:
geolocation=*
This negates the entire purpose.
3. Trusting third-party domains blindly
Allowing:
payment=(self "https://third-payment.com")
Opens risk if the vendor is compromised.
4. Not reviewing policies after adding new integrations
Features get added without policy updates, creating drift.
5. What Permissions-Policy Does Not Protect Against
It does NOT stop:
- Script injection (CSP/Trusted Types do that)
- Third-party script compromises
- DOM manipulation
- Token theft
- Extension-based attacks that operate outside policy
- AI assistant overlays (some aspects bypass it)
Permissions-Policy is powerful — but only for specific APIs.
This is why runtime monitoring must exist alongside it.
7. How BreachFin Complements Permissions-Policy
Permissions-Policy blocks dangerous API calls.
BreachFin detects:
- Attempted API misuse
- Scripts probing restricted APIs
- Extension interference patterns
- DOM changes aligned with blocked actions
- Invisible manipulation before policy enforcement
- Behavior drift that hints at compromised scripts
Together:
- Permissions-Policy reduces attack surface
- BreachFin monitors execution and detects misuse
- Both provide compliance-grade visibility
This creates a complete control — preventive + detective.
Final Takeaway
Permissions-Policy is one of the most powerful browser security headers — yet the least deployed.
It protects users from:
- Data theft
- Device API abuse
- Browser-level phishing
- Clipboard and token exposure
- Malicious iframe and extension behavior
But it cannot provide visibility, alerting, or runtime drift detection.
That’s why modern security requires:
- CSP + SRI + Trusted Types (prevention)
- Permissions-Policy (restriction)
- BreachFin runtime monitoring (detection)
