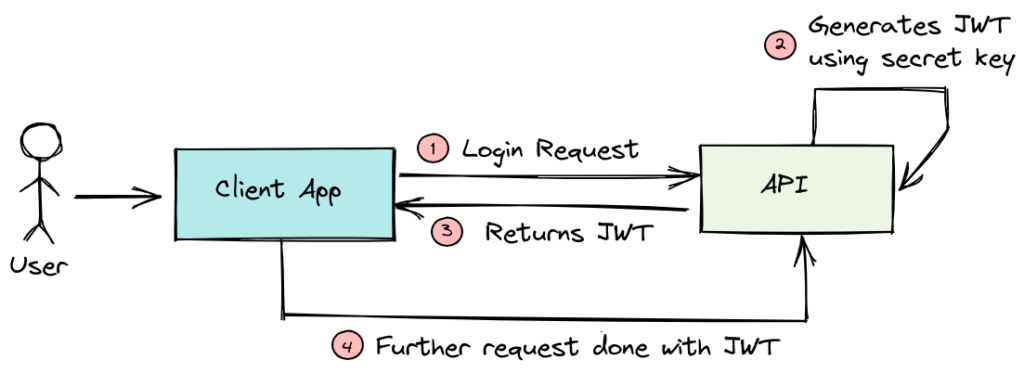
JSON Web Tokens (JWTs) are everywhere — APIs, SaaS platforms, mobile apps, and modern authentication systems rely on them for stateless identity and authorization.
Yet JWTs are also one of the most commonly misused security mechanisms, leading to account takeovers, token theft, and large-scale breaches.
This guide explains how to use JWT correctly, what not to do, and how to align JWT usage with modern security and compliance expectations.
What JWT Is (and What It Is Not)
A JWT is a signed token that carries claims about an authenticated user or system. It consists of:
- Header – algorithm and token type
- Payload – claims (user ID, roles, expiry, etc.)
- Signature – cryptographic integrity protection
JWT is:
- Stateless
- Verifiable without database lookups
- Ideal for APIs and distributed systems
JWT is not:
- A session replacement for browsers without safeguards
- A secure storage mechanism
- Encrypted by default
Common JWT Anti-Patterns (Avoid These)
- Long-lived access tokens
- Storing JWTs in localStorage
- Using JWTs as session cookies without CSRF protection
- No refresh token rotation
- Reusing signing keys across environments
- Trusting decoded tokens without verification
Most real-world JWT breaches trace back to one of these mistakes.
JWT, Compliance, and Modern Threats
From a compliance perspective (PCI DSS, SOC 2, ISO 27001):
- JWT misuse can lead to authentication control failures
- Token theft enables account takeover and fraud
- Poor token handling violates secure session management requirements
Modern attacks target:
- Browser-executed tokens
- JavaScript-accessible storage
- Third-party script injection
How BreachFin Helps
JWT security does not stop at backend validation.
BreachFin focuses on where JWTs are most often compromised:
- Browser execution
- Client-side scripts
- Shadow integrations and injected code
BreachFin helps organizations:
- Detect unauthorized scripts accessing tokens
- Identify risky client-side behaviors
- Enforce browser-side visibility aligned with modern compliance needs
Because the strongest JWT implementation still fails if the browser is compromised.
Final Takeaway
JWT is powerful, efficient, and scalable — when used correctly.
To use JWT the right way:
- Short-lived access tokens
- Secure refresh token handling
- Strong signing algorithms
- Minimal payloads
- Strict validation
- Browser-side protection
JWT is not insecure.
Misusing JWT is.
If your authentication relies on JWT, make sure your security strategy extends beyond the backend — into the browser, where modern attacks actually happen.
